The Buzz on Risk Management Enterprise
Table of ContentsSome Of Risk Management EnterpriseWhat Does Risk Management Enterprise Do?Get This Report about Risk Management Enterprise
Control who can see or edit these aspects by establishing particular gain access to legal rights for private customers, making certain details protection and tailored usability. Permits customers to customize their user interface by selecting and preparing crucial data elements. Gives a personalized experience by enabling customization of where and how data elements are shown.It permits access to real-time incorporated data promptly. Facilities can use extensive information knowledge for quicker and much more informed decision-making.

Diligent is a risk administration software application that enables maximizing performance, and improves growth. It additionally aids keep track of risks with ERM software application that includes integrated analytics and adapts to your organization demands.
A Biased View of Risk Management Enterprise
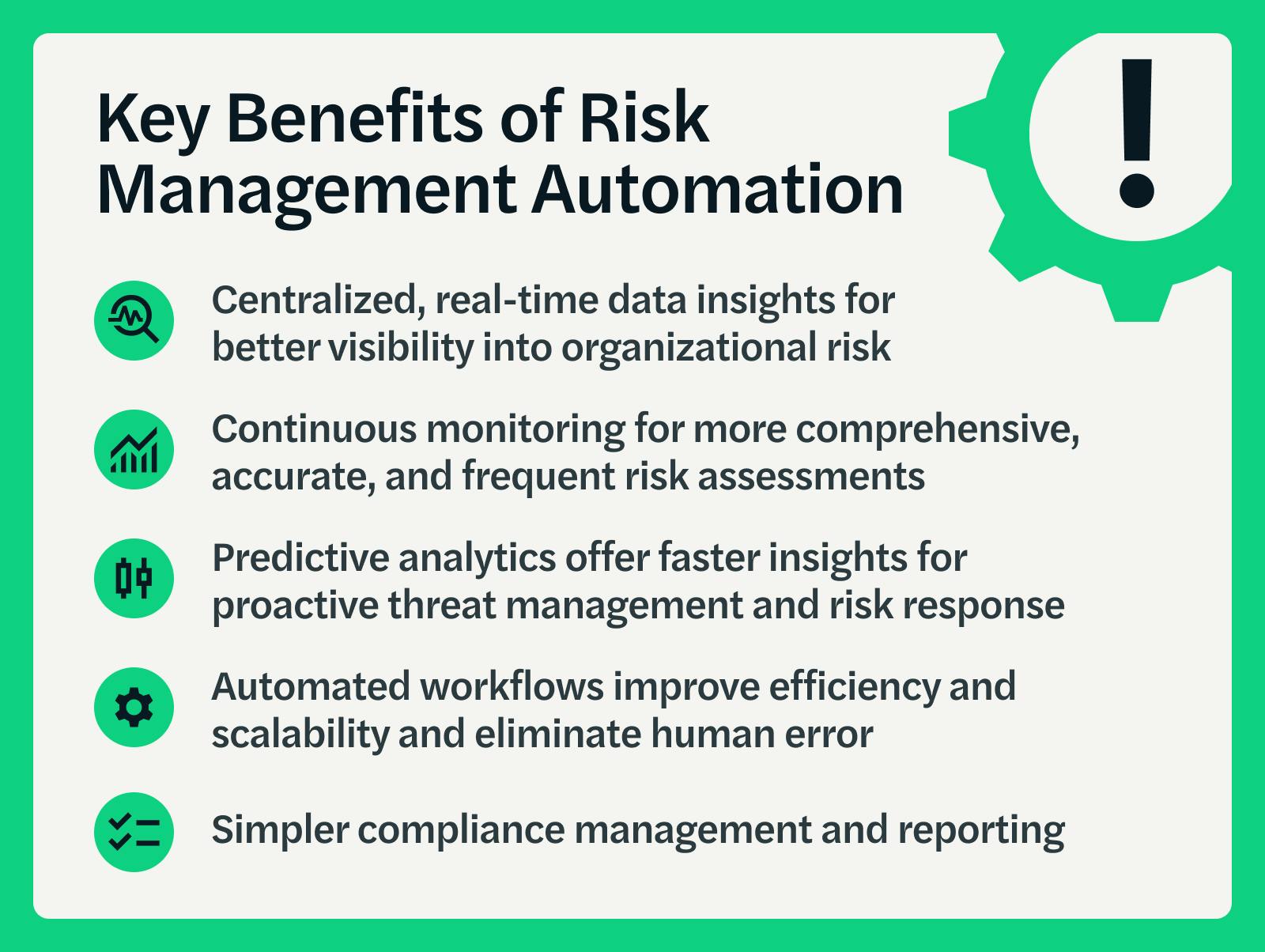
It likewise offers one-click reports. It offers your management and board the real-time understandings they need. Simplifies the process of accumulating risk information from numerous parts of the organization. Risk Management Enterprise. It enables very easy modification of records and storyboards. Provides leadership and the board with real-time danger insights. Usage ACL's advanced analytics to detect danger patterns and anticipate hazards.
This allows firms to catch danger insights and Your Domain Name red flags in the third-party supplier's safety go to website report. This enables conserving threat assessments as auditable records. It additionally enables exporting them as PDFs. To complete the procedure companies can finish a review date. Enables firms to catch and record risk understandings and red flags in third-party vendor safety and security records.
It also lowers threat with streamlined conformity and threat management. It can help collect and track all your risks in the Hyperproof danger register.
It offers quick access to essential info and documents. This makes certain the safety More about the author and security of Active evidence instances by making it possible for multi-factor verification (MFA) making use of authenticator applications such as Google Authenticator, Microsoft Authenticator, or Authy.
The Greatest Guide To Risk Management Enterprise

It offers top-tier security attributes to secure sensitive information. This risk administration software is an ideal tool for facilities looking to fix unnecessary problems or risks.
Customers can also make use of the AI-powered tools and pre-existing material to develop, assess, prioritize, and address risks effectively. Simplifies the process of configuring and inhabiting threat registers.